Modern Air Defence Must Include Mobile Network Intelligence
Abstract
The increasing use of drones in hybrid warfare has exposed a critical and under-addressed vulnerability in national security: the exploitation of civilian mobile networks for command, control and surveillance by hostile unmanned aerial systems (UAS). This article examines the emerging threat posed by drones that operate beyond visual line of sight (BVLOS) using LTE/5G infrastructure, often appearing indistinguishable from legitimate mobile devices. Recent incidents in Ukraine and across multiple NATO member states—including Denmark, Germany and Lithuania—highlight the growing prevalence of this tactic. Mobile networks, designed to serve users on the ground, frequently provide unintended coverage at altitude, enabling persistent drone operations deep inside national airspace. The paper advocates for strategic action by governments to assess their exposure, including airborne signal surveys at various altitudes and along key national corridors. It further argues that telecom infrastructure should be leveraged as a defensive sensor layer, enabling early detection and attribution of drone activity through network-level behavioural analysis. This approach represents a vital evolution in air defence strategy and must be integrated into national and alliance-level planning to counter the modern drone threat effectively.
An Enemy Enabled by Mobile Networks
Russia’s overnight bombardment of Ukraine, involving over 500 drones and dozens of missiles, was one of the most intense aerial assaults in recent months. Yet beneath the noise of explosions and intercepts lies a quieter, more insidious threat: the use of mobile networks by hostile drones for command, control and surveillance.
These drones are not necessarily relying on military satellite systems. Increasingly, they are equipped with ordinary SIM cards and are connecting to the same mobile networks used by the civilian population. In doing so, they blend invisibly into national infrastructure, transmitting video feeds, receiving instructions, and coordinating missions while appearing—on the surface—no different to a smartphone or internet-connected device.
Without further analysis, this activity is virtually indistinguishable. But with the right detection frameworks, the patterns of behaviour exhibited by these drones—such as the manner in which they move between cell towers as a result of their altitude and other factors—can be identified and flagged in real-time for investigation.
A New Domain of Hybrid Threat
This issue is no longer confined to Ukraine. In recent days, suspicious drone activity has disrupted airspace in Denmark, Norway, Germany, Lithuania and Poland. Danish authorities were forced to close civil airspace over Karup Airbase—home to the country’s helicopter fleet and airspace surveillance systems—after drones were observed overhead. Other military installations were also targeted, though not publicly named.
Denmark’s defence minister has described these incursions as a likely hybrid attack, the work of a professional actor. Meanwhile, similar sightings have occurred over military airbases in Norway, F-35 facilities, and border regions of Germany. Flights at Vilnius airport in Lithuania were delayed after drones were spotted, and both Estonia and Poland have raised concerns over breaches of their airspace by Russian aircraft and unmanned systems.
While these incidents may differ in nature, they all point to a common vulnerability: mobile networks, originally built to serve people on the ground, are being exploited from the air.
Understanding the Vulnerability
It is essential that nations understand how exposed their mobile networks are to this form of misuse. These networks were designed to provide coverage to users at ground level, not to airborne platforms hundreds of metres above. Yet in many cases, the signal reach of a mobile tower extends vertically much further than required, inadvertently providing connectivity at altitude that drones can exploit.
Assessing this vulnerability should be treated as a national security priority. Countries must begin surveying their own airspace to determine where and at what altitudes their mobile infrastructure is accessible to airborne devices. This effort should focus initially on border regions and coastlines, where drones may enter from neighbouring territories, but must also extend to the airspace surrounding, and en route to, critical infrastructure—military bases, energy facilities, data centres, government buildings, and transport hubs.
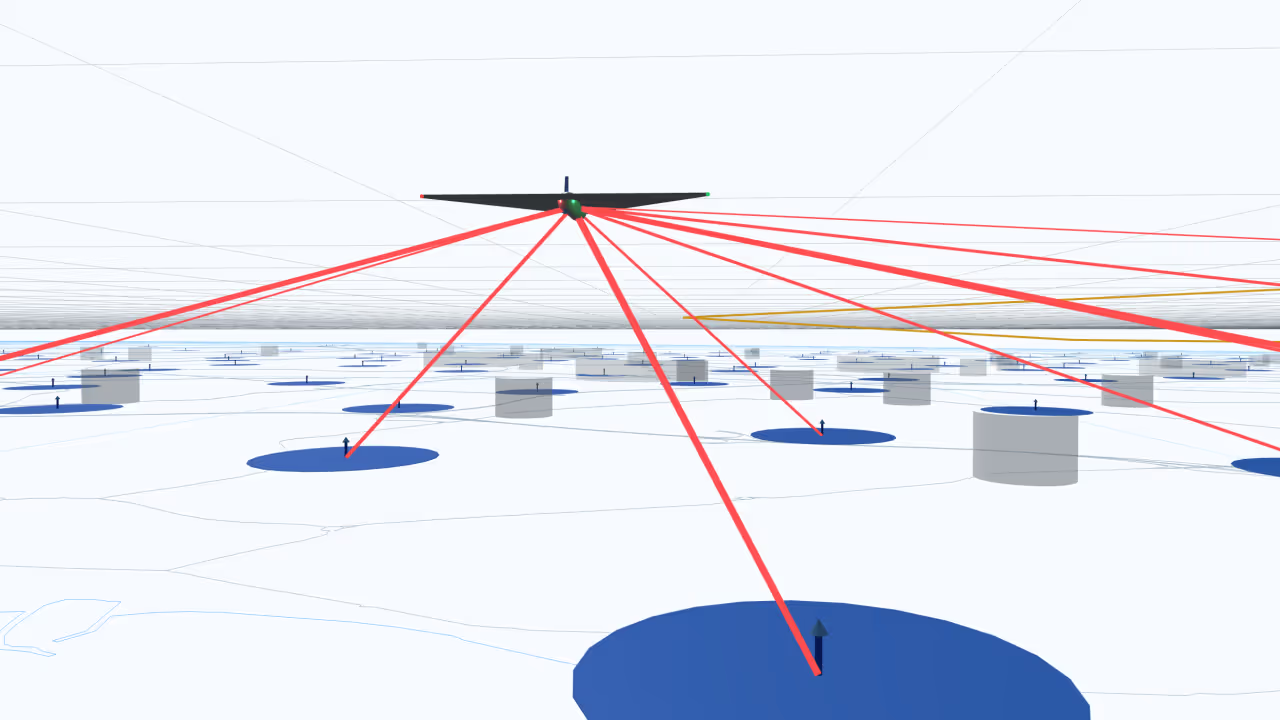
Surveys should be conducted using light aircraft or other airborne platforms, flying routes at various altitudes—for example up to 3000 metres above ground level—to assess real-world mobile signal coverage. The findings will provide a data-driven foundation for countermeasures, allowing governments to reshape coverage, prioritise surveillance of high-risk zones, or take steps to deny airborne access in certain areas.
Seeing the Threat Before It Strikes
Once the vertical coverage profile of a mobile network is understood, it becomes possible to use the network itself as a defensive tool. While a drone may initially appear to be a regular device, the way it moves through the network, transitions between towers, and behaves in flight often differs markedly from a person using a phone on the ground or in a vehicle.
With appropriate safeguards and technical capability, telecom infrastructure can be used to identify these differences. This form of analysis does not rely on inspecting message content or decrypting communications. Instead, it examines metadata and signalling behaviour—the digital equivalent of spotting an aircraft based on its flight pattern, rather than its payload.
This approach offers a critical early-warning layer that can complement radar systems and airspace surveillance. By detecting hostile drones at the moment they begin using a domestic mobile network—often well before they reach their target—countries can gain the time needed to investigate, respond or disrupt.
A Necessary Shift in Defence Thinking
Drones have changed the shape of modern warfare. They are small, cheap, fast-moving and increasingly autonomous. But it is their use of ubiquitous civilian infrastructure that makes them especially dangerous—and especially difficult to detect.
Defending against these systems requires more than kinetic interceptors. It demands an understanding of how networks are being used, where that usage poses a threat, and what can be done to see these silent incursions before it is too late.
A drone’s reliance on mobile networks does not only present a threat—it also creates an opportunity. By using public infrastructure for command, control and video transmission, the drone increases its attack surface and exposes itself to monitoring, disruption and denial. This dependency becomes a vector through which defenders can respond. In this way, the very networks being exploited can also be leveraged as defensive assets—providing early warning, actionable intelligence, and a means to strike back through the infrastructure the drone depends on.
This is not an abstract or future concern. It is already happening—in Ukraine, across Europe, and above some of NATO’s most important facilities.
If we continue to ignore the role that mobile networks play in enabling drone operations, we risk leaving a critical part of our airspace undefended. It is time to treat mobile networks not only as infrastructure to be protected, but as a domain through which hostile activity can be observed, analysed and, ultimately, countered.
