Non-Kinetic Options for Drone Countermeasures (CUAS): The MAVLink Exposure in Mobile Networks
MAVLink is ubiquitous across the unmanned aerial systems (UAS) ecosystem. Its compact frame, efficient telemetry structure and cross-stack compatibility have made it the de facto choice for many hobbyist, commercial and mission-grade platforms. That ubiquity, however, hides an important operational exposure: MAVLink commonly lacks built-in encryption and strong authentication, leaving messages vulnerable when they traverse networks that can be observed or manipulated.
Recent research (Hamza et al., 2024) of the protocol has examined UAV–GCS communications and identified these exact vulnerabilities: the absence of mandatory encryption and authentication exposes MAVLink to eavesdropping, man-in-the-middle attacks, unauthorised access and denial-of-service. These threats can undermine the confidentiality, integrity, availability and authenticity of C2 and telemetry links. Although there are ongoing proposals and lightweight cryptographic techniques, message-signing options in later protocol versions, and other mitigations, real-world deployments remain uneven — especially for MAVLink traffic that is carried in the clear over IP on commercial mobile networks.
Why the 4G LTE/5G use case matters
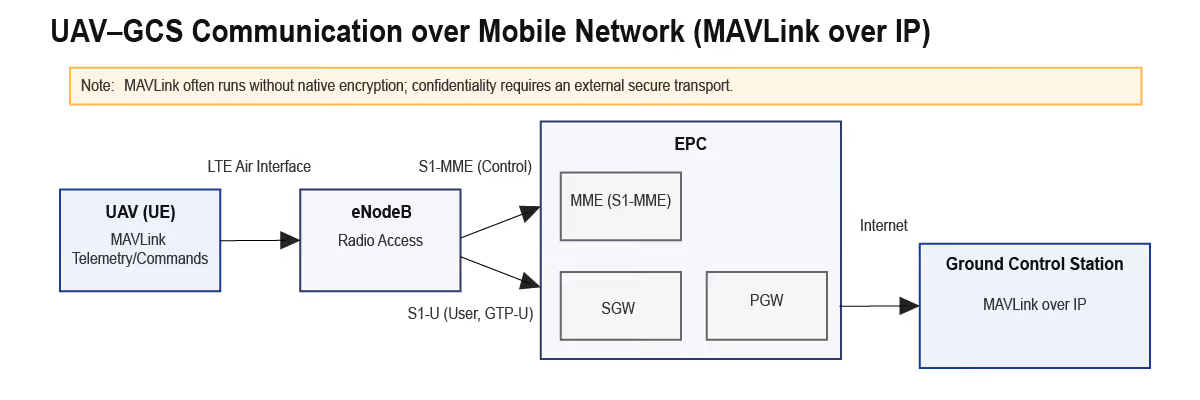
This article is explicitly about MAVLink when it is carried over an 4G LTE or 5G mobile network connection — i.e. MAVLink packets encapsulated in IP and traversing operator networks (user-plane tunnels such as GTP-U). Many BVLOS drones use cellular links for persistent C2 and video uplink; when that traffic is unprotected, two technical facts combine to create a conceptual defensive option:
- Unprotected MAVLink over IP. MAVLink streams over cellular are often transported as plaintext IP packets (UDP is common; TCP is also used). Unless optional message signing is enabled and an encrypted transport is used, messages are not cryptographically authenticated or confidential. An on-path observer can read telemetry and, in principle, emulate controller messages.
- Mobile network signalling and packet data. LTE and 5G separate control and user planes. Control-plane signalling interfaces surface attach, handover and context events; user-plane tunnels carry IP flows and use identifiers (TEIDs in LTE) to identify sessions. With lawful interception providing mirrored signalling feeds from a mobile operator, those artefacts can be correlated to identify which user-plane flows carry a given UE’s command-and-control (C2) or video.
The conceptual chain (Detect → Map → Position → Impersonate)
Bringing those facts together yields a simple conceptual chain — stated at a policy/architecture level rather than as an operational recipe:
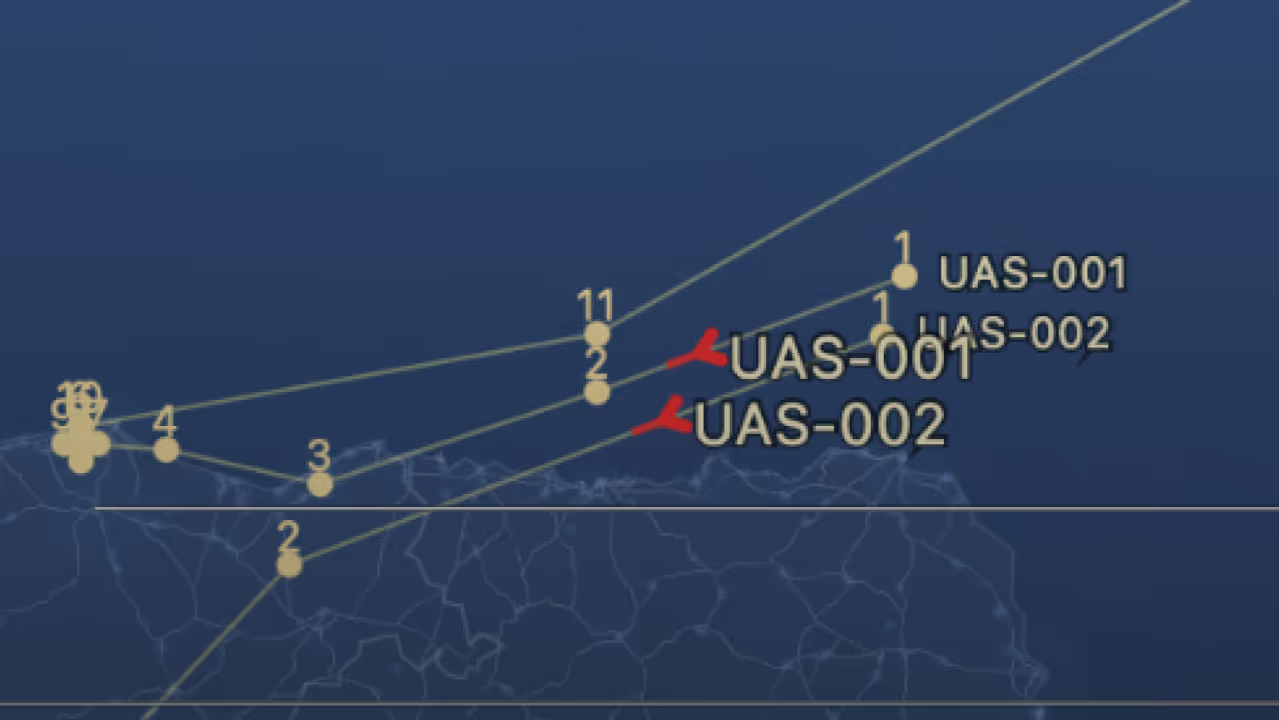
• Detect: use signalling feeds and anomaly detectors to flag sessions that behave like airborne UEs (rapid or atypical handovers, cell geometry inconsistent with terrestrial movement, unusual TA/ECI patterns).
• Map: correlate control-plane artefacts to user-plane identifiers so the precise data session and its external endpoints are known (for example via TEID ↔ IP correlation in LTE).
• Position: with authorised, operator-approved visibility, the defender gains situational awareness of the session and the endpoint(s) involved.
• (Conceptual) Control/Impersonate: where a platform accepts unauthenticated commands, an alternate endpoint that presents itself as the controller could — in principle — be offered to the drone.
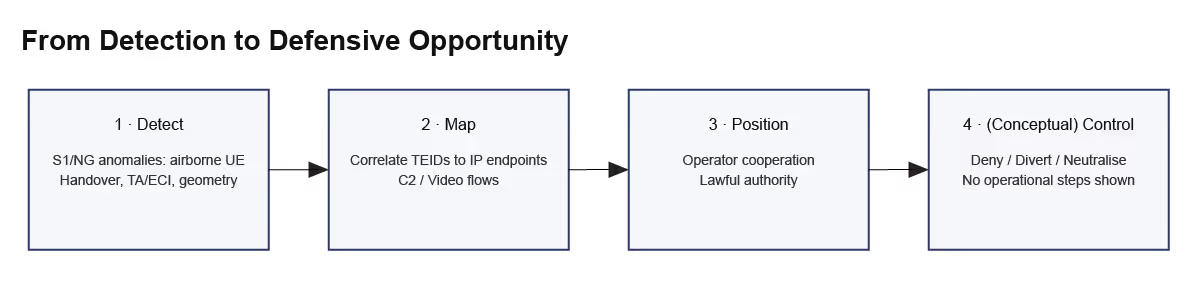
It is essential to stress this is conceptual: the “control/impersonate” step is a statement of theoretical possibility when the technical preconditions are met, not a how-to guide. The operational or implementation details are out of scope of this article.
Operational appeal and forensic value
Why would planners be interested? The appeal is twofold:
- Non-kinetic reach: an analyser that uses operator signalling feeds can provide broad geographic reach across covered areas without requiring extensive fielded RF sensor deployments. For drones that rely on commercial cellular C2 links, this offers persistent coverage where the network exists.
- Forensic artefacts: correlating control-plane and user-plane records yields durable artefacts — session IDs, TEIDs, external IP endpoints, timestamps and handover sequences — that aid attribution, timeline reconstruction and downstream intelligence tasks.
Practical limits and technical caveats
The conceptual option is bounded by clear technical limits:
- Protocol variants and mitigations: MAVLink-2’s optional message signing, when enabled and properly managed, reduces the feasibility of naive impersonation. Message signing provides authentication but not confidentiality.
- Encrypted transports: MAVLink over TLS, VPNs or radio ciphers substantially raises the bar to passive observation or injection.
- Alternative connectivity: Drones using satellite/NTN links, proprietary encrypted radios or bespoke C2 methods are outside the 4G LTE/5G threat model described here.
- Adversary adaptation: Operators or adversaries may shift endpoints, adopt encryption, move to other transports or use obfuscation—so any technical advantage is transient without continuous adaptation.
- Safety: Acting on an airborne platform risks uncontrolled behaviour and safety incidents; safety considerations are paramount.
Conclusion
MAVLink’s absence of mandatory authentication and encryption across many deployments is a systemic vulnerability; when such traffic traverses 4G/5G operator networks and a defender has authorised visibility of signalling and packet data, a conceptual, non-kinetic option exists to present an alternate ground-control endpoint (GCS) — and, under narrow technical preconditions, impersonation and resultant platform takeover remain theoretical possibilities.
Clarifying Notes
- MAVLink security: MAVLink v1 has no built-in authentication or encryption. MAVLink 2 introduced message signing (authentication) but payloads are still transmitted in plaintext unless placed inside an encrypted transport (VPN, TLS, radio cipher).
- Transport usage: MAVLink is transport-agnostic and most commonly used over serial links or UDP; TCP and radio-modem transports are also seen in the field.
- Mobile-network architecture: In LTE, S1-MME carries signalling (S1AP over SCTP) while S1-U carries user data (GTP-U over UDP, identified by Tunnel Endpoint Identifiers, TEIDs). 5G employs analogous N2 (control) and N3 (user-plane) interfaces.
Reference: Hamza, M., Mohsin, M., Khalil, M., & Kazmi, S. M. K. A. (2024). MAVLink Protocol: A Survey of Security Threats and Countermeasures. ICoDT 2024. DOI: 10.1109/ICoDT262145.2024.10740195.
Glossary
AMF (Access and Mobility Management Function)
A 5G Core Network function responsible for signalling and mobility management between the user equipment (UE) and the network’s control plane. The 5G equivalent of the LTE MME.
C2 (Command and Control)
The communication link through which a ground operator sends commands to a drone and receives telemetry feedback (position, status, etc.).
C-UAS (Counter-Unmanned Aerial System)
Technologies and measures used to detect, track, identify, and mitigate threats from hostile or unauthorised drones.
EPC (Evolved Packet Core)
The core network architecture of LTE. It consists of key components such as the MME, SGW, and PGW that manage user sessions and data transport.
eNodeB (Evolved Node B)
The LTE base station that connects user equipment (UE) to the core network. In 5G the equivalent node is the gNodeB.
GCS (Ground Control Station)
The system or software interface used by a drone operator to monitor and control UAV flight via telemetry and command messages. Often communicates using MAVLink.
GTP (GPRS Tunnelling Protocol)
Protocol used in LTE and 5G to carry user data across the mobile core network.
- GTP-C handles control signalling.
- GTP-U carries user-plane traffic (actual data packets).
GTP-U (GPRS Tunnelling Protocol – User Plane)
Encapsulates user IP traffic between eNodeB/gNodeB and gateways (SGW/UPF). Each tunnel is uniquely identified by a TEID (Tunnel Endpoint Identifier).
LTE (Long-Term Evolution)
4G mobile-network technology providing broadband data connectivity. Forms the basis for many UAV command links when drones use SIM-based connectivity.
MAVLink (Micro Air Vehicle Link)
A lightweight, open communication protocol for exchanging commands and telemetry between UAVs and ground stations.
- MAVLink v1: no authentication or encryption.
- MAVLink v2: adds optional message signing (authentication only).
MME (Mobility Management Entity)
LTE control-plane function responsible for mobility management, bearer setup and session control. The 5G equivalent is the AMF.
NG (Next Generation Interface)
The family of interfaces connecting 5G base stations (gNodeBs) to the 5G Core. Analogous to LTE’s S1 interfaces.
- N2: control plane (signalling).
- N3: user plane (data tunnels).
PGW (Packet Data Network Gateway)
Component of the LTE EPC that connects the mobile network to external IP networks, assigning IP addresses to UEs and enforcing policy.
RAN (Radio Access Network)
The radio portion of a mobile network connecting UEs (such as UAV modems) to base stations (eNodeB/gNodeB).
S1 Interface
The interface between the LTE eNodeB and the core network (MME/SGW).
- S1-MME: carries control-plane signalling (S1AP over SCTP).
- S1-U: carries user-plane data (GTP-U over UDP).
S1AP (S1 Application Protocol)
Protocol used over the S1-MME interface to manage signalling messages (attach, detach, handover, context updates) between the eNodeB and MME.
SGW (Serving Gateway)
LTE EPC function that routes and forwards user data packets and maintains data paths between eNodeBs and the core network.
TEID (Tunnel Endpoint Identifier)
A 32-bit identifier used in GTP-U tunnels to distinguish individual user sessions. Each active data bearer has a unique TEID in each direction.
UE (User Equipment)
The end-device connected to the mobile network — in this context, a drone equipped with a cellular modem or SIM.
UAV (Unmanned Aerial Vehicle)
An aircraft operated without a human pilot onboard. Often referred to as a drone.
UPF (User Plane Function)
5G Core element that handles user-plane data forwarding, QoS enforcement and IP address allocation — the 5G equivalent of the LTE PGW/SGW user-plane roles.
User Plane
The path that carries the actual user data (IP traffic). In LTE this is S1-U (GTP-U); in 5G it is N3 (GTP-U).
Control Plane
The set of signalling channels and procedures that manage sessions, authentication, mobility and bearer setup. In LTE this is S1-MME; in 5G it is N2.
VPN (Virtual Private Network)
An encrypted tunnel that protects network traffic from interception and eavesdropping. Often used to secure MAVLink communications over IP.
TLS (Transport Layer Security)
Cryptographic protocol providing encryption and authentication for IP traffic. MAVLink can be encapsulated in TLS sessions to mitigate exposure.
NTN (Non-Terrestrial Network)
An extension of mobile network standards (e.g. 3GPP Release 17) to support satellite-based connectivity, allowing UAVs to maintain links beyond terrestrial coverage.
Non-Kinetic Countermeasure
A defensive action that does not use physical force (e.g. electronic, cyber or information-based disruption) to neutralise or deter a threat.
